Material’s new OAuth Remediation Agent shrinks your attack surface by automating the discovery and cleanup of risky third-party apps and AI agents across your cloud workspace.
Security teams have spent years hardening the front door. But while the door is bolted, the windows are wide open. In the modern cloud workspace, that window is OAuth.
The problem isn't just that users are granting permissions to third-party apps—it’s the sheer volume of it. Between the explosion of SaaS and the unprecedented rate of adoption of AI agents, security teams are facing an impossible operational burden. Every new productivity tool and LLM-backed bot requires a handshake with your corporate data. The result is an explosion of app connectivity that most teams are currently tracking via spreadsheet—if they’re tracking it at all.
To make matters worse, OAuth connections fall outside of most companies’ TPRM processes, meaning they get little to no vetting at all — even though they have the most access to data.
How do you keep the organization and its data secure without slowing down your team by denying cutting-edge tools?
That’s where Material steps in: enabling AI adoption while reducing risk with our intelligent OAuth Threat Remediation Agent.
The operational trap of manual reviews
Most organizations recognize the risk. In our recent research, 80% of teams called automating OAuth risk a priority, yet nearly half admitted they’ve neglected it. And another third are relying solely on manual reviews that don’t scale.
The reason for this mismatch is the untenable operational burden of reviewing every app connection and auditing it on an ongoing basis. An analyst might vet an app today, but they can’t realistically re-audit it every month to see if its scope has crept or its behavior has changed. The result is a massive, unmanaged attack surface where trusted apps like Salesloft or a random "AI Productivity Bot" become permanent backdoors into your most sensitive data.
Introducing the OAuth Threat Remediation Agent
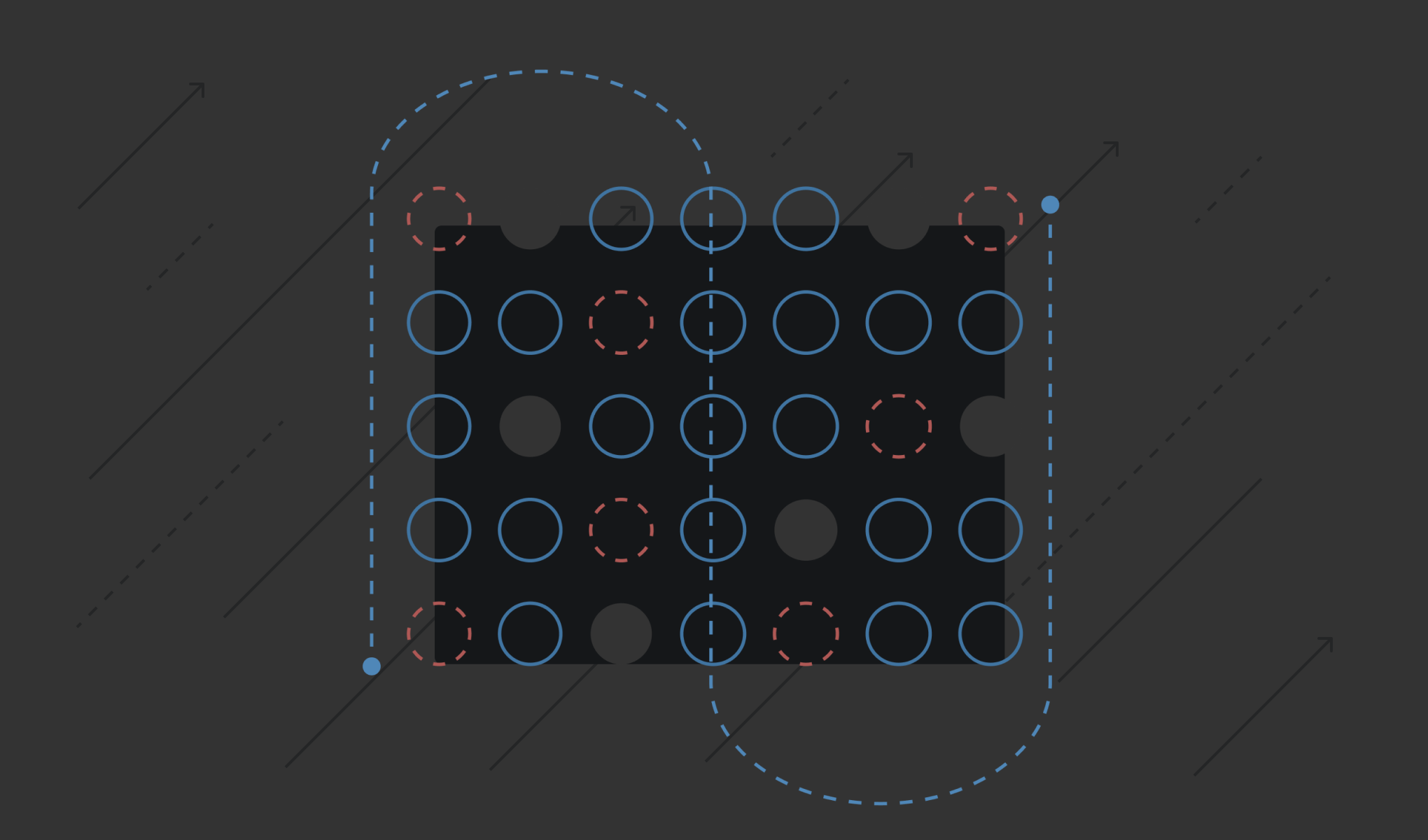
Today, we’re adding a new capability to Material designed to do the tedious work of a security analyst, but autonomously and in real time. The Material OAuth Remediation Agent doesn't just list what’s connected; it actively manages the lifecycle of every integration across your cloud workspace.
The agent goes deeper than other tools can, while also handling the grunt work that usually burns out security teams–or is simply far too large to tackle in the first place:
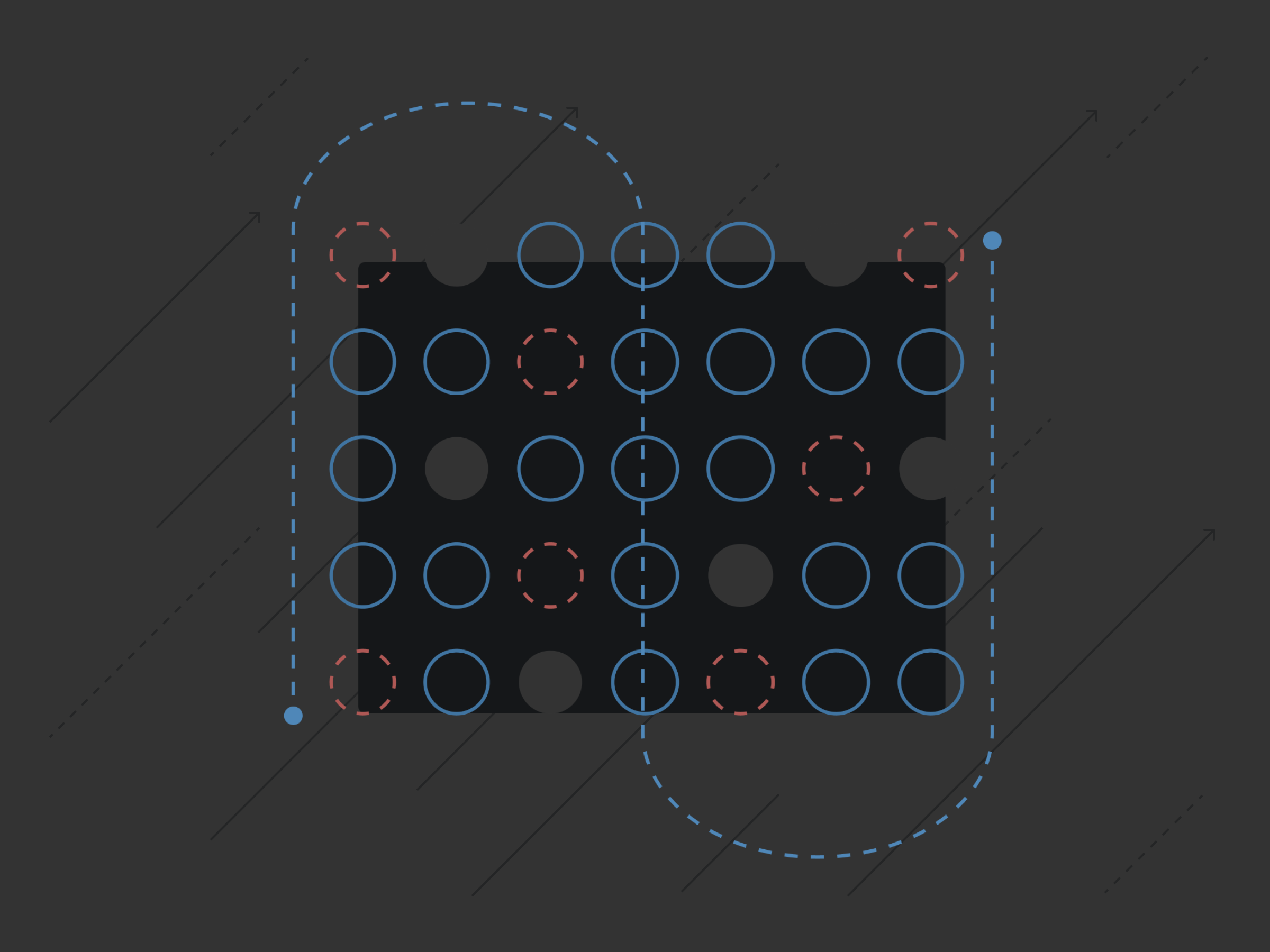
- Constant Discovery: Identifying every new app the second a user clicks "Allow."
- Contextual Risk Assessment: Evaluating the app’s actual behavior and its "blast radius" based on who authorized it and what they have access to to automatically classify an app as Malicious, Risky or Allowed
- Automated Cleanup: Identifying and revoking dormant or over-privileged apps that haven't been used in months.
Beyond static reviews: Why deep integration matters
There are plenty of tools that can read a static list of permissions or check a vendor’s reputation. But a permission list only tells you what an app could do, not what it is doing. Material uses deep integration into the cloud workspace to understand the context of a given OAuth connection - both the user requesting it and the app’s actual behavior. And if an app is risky, it doesn’t just alert, it responds automatically by revoking tokens.
Real-time app behavior
We look at the actual API calls an OAuth app makes. If a simple integration suddenly starts making unusual calls to your sensitive Drive folders or exporting large volumes of data, the agent sees it. This isn't a "point-in-time" scan—it’s continuous auditing of the app’s actual behavior within your environment.
User blast radius
Risk is relative. An OAuth app granted access by a DevOps lead with global admin rights is a much larger problem than the same app connected by a BPO worker with limited data access. Material correlates app permissions with user identity and data context to prioritize the threats that actually matter.
Automatic revocation
You set the level of automation for the agent: it can actively manage app connections by automatically revoking tokens for risky or dormant apps. For ambiguous or necessary app usage, it crowdsources investigation with decentralized verification via Slack to let users confirm use and justify their app access. And it keeps a human in the loop for any mission-critical apps, prioritizing threats that matter by correlating app permissions with user identity and data context, surfacing the most critical risks for human review.
Scaling security for the AI era
The rise of AI has made this a "now" problem. Every new AI tool requires a handshake with your workspace. Without a way to automate the vetting and monitoring of these handshakes, you're effectively operating without a perimeter. It’s harder to accept the good when you can’t tell what’s bad.
The OAuth Threat Remediation Agent acts as a force multiplier. It allows security teams to:
- Automate the tedious: Let the agent handle the initial vetting and ongoing monitoring.
- Kill threats instantly: Use the automated "kill switch" to revoke tokens the moment an app's behavior deviates from the norm.
- Empower users: Use decentralized verification (via Slack or email) to let users justify their app usage, taking the "toil" off the security desk.
Security that works
We aren’t interested in giving you another dashboard to ignore. We’re giving you an agent that does the work for you. By moving from static inventory to dynamic, behavior-based remediation, Material helps you close the OAuth backdoor for good.
We’ll be demoing these new capabilities at SecureWorld Boston on April 8–9. If you want to see how deep integration changes the way you manage OAuth risk, get in touch with us today.