New research from Material reveals a growing gap between awareness and action in OAuth security, as organizations struggle to manage app access, automation, and emerging risks like AI agents.
We recently surveyed 45 security leaders to better understand how organizations are managing OAuth applications, a key capability of the cloud workspace and a critical layer in modern attack chains. It’s easier than ever to execute an attack via a malicious OAuth grant or to hijack a legitimate but overpermissioned one, giving attackers persistent backdoor access to company data. Material’s findings point to a growing gap between awareness of the problem and the ability to automatically address this issue at scale.
The Findings: A Gap Between Priority and Preparedness
Our research reveals three key trends:
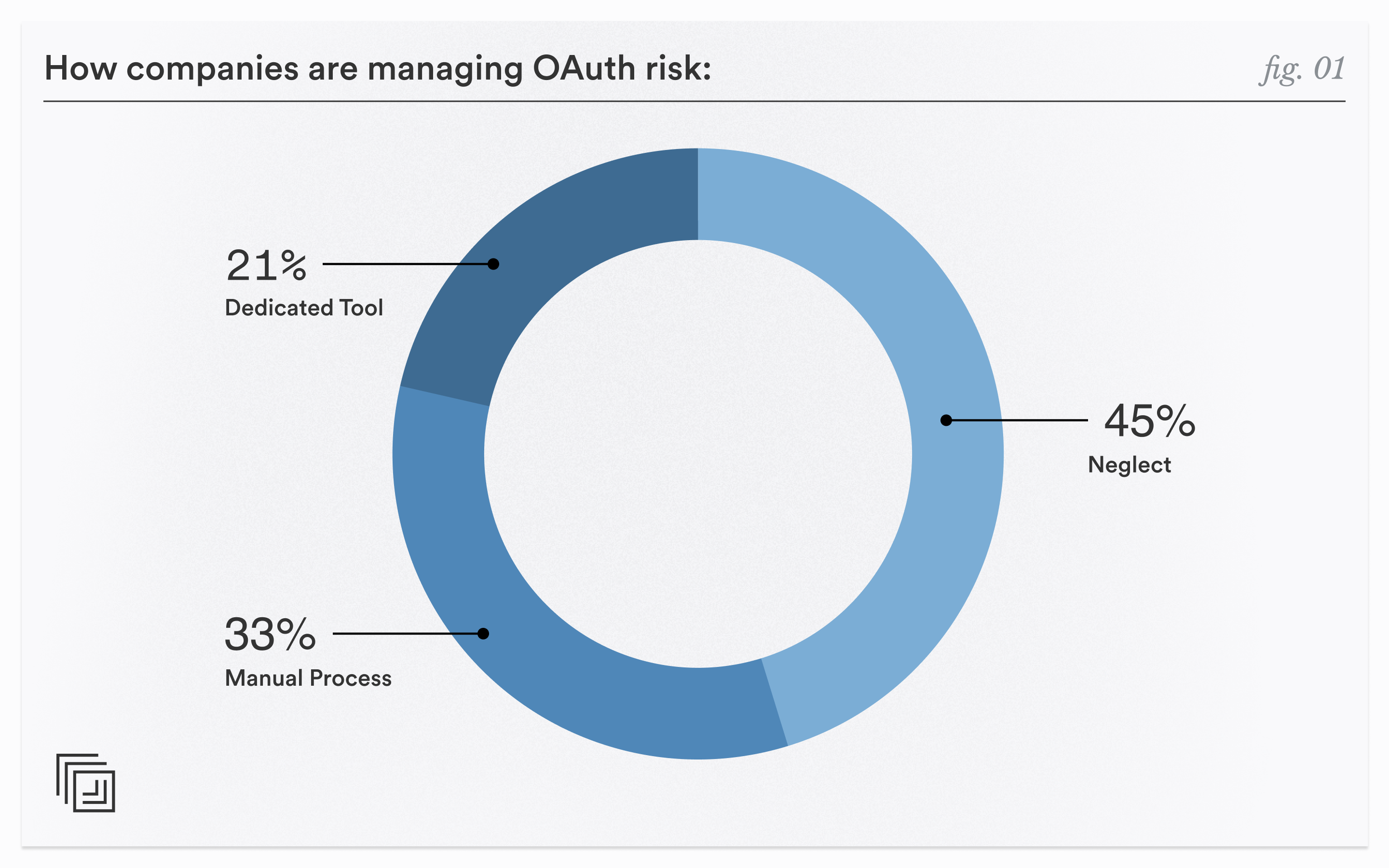
- Lack of structured control over OAuth apps: Nearly half of respondents (45%) report that they’re neglecting OAuth app governance, while 33% are still relying on manual processes. Only a small minority have implemented dedicated tools or automated controls.
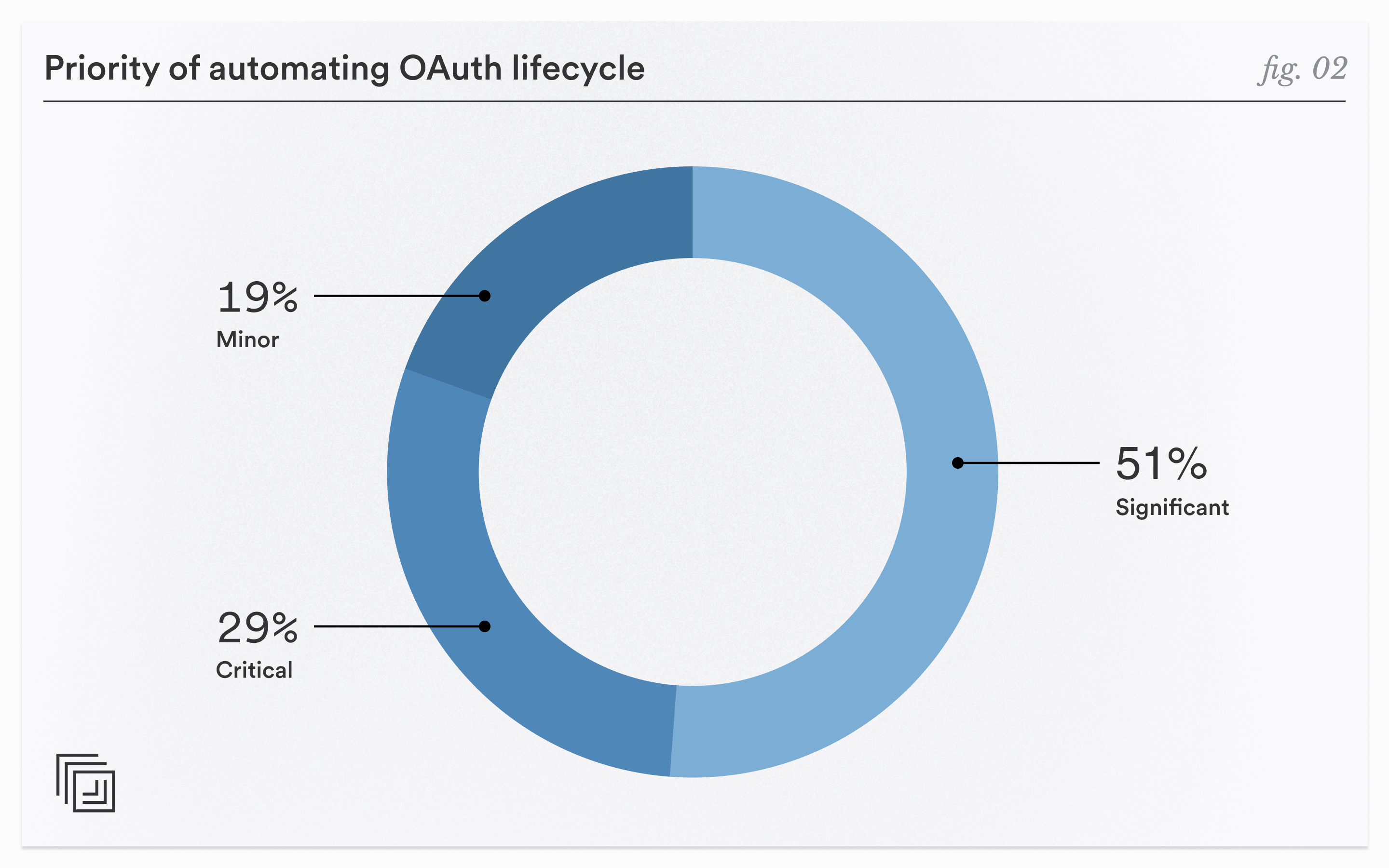
- Automating this process is a challenge: 80% of respondents rated this capability as a “significant” or “critical” priority.
- Exposure still exists across all maturity levels: Even when they did have a tool in place, 67% of respondents still reported elevated concern. This signals that dedicated tools aren’t solving the underlying problem, and there’s a gap between the ability to simply monitor and the ability to fix errant OAuth grants.
The Evolution of Attack Chains
These findings reflect a broader shift in the reality of how attacks unfold. Modern threats rarely stop at initial access. Instead, they follow a chain that takes them across the cloud workspace:
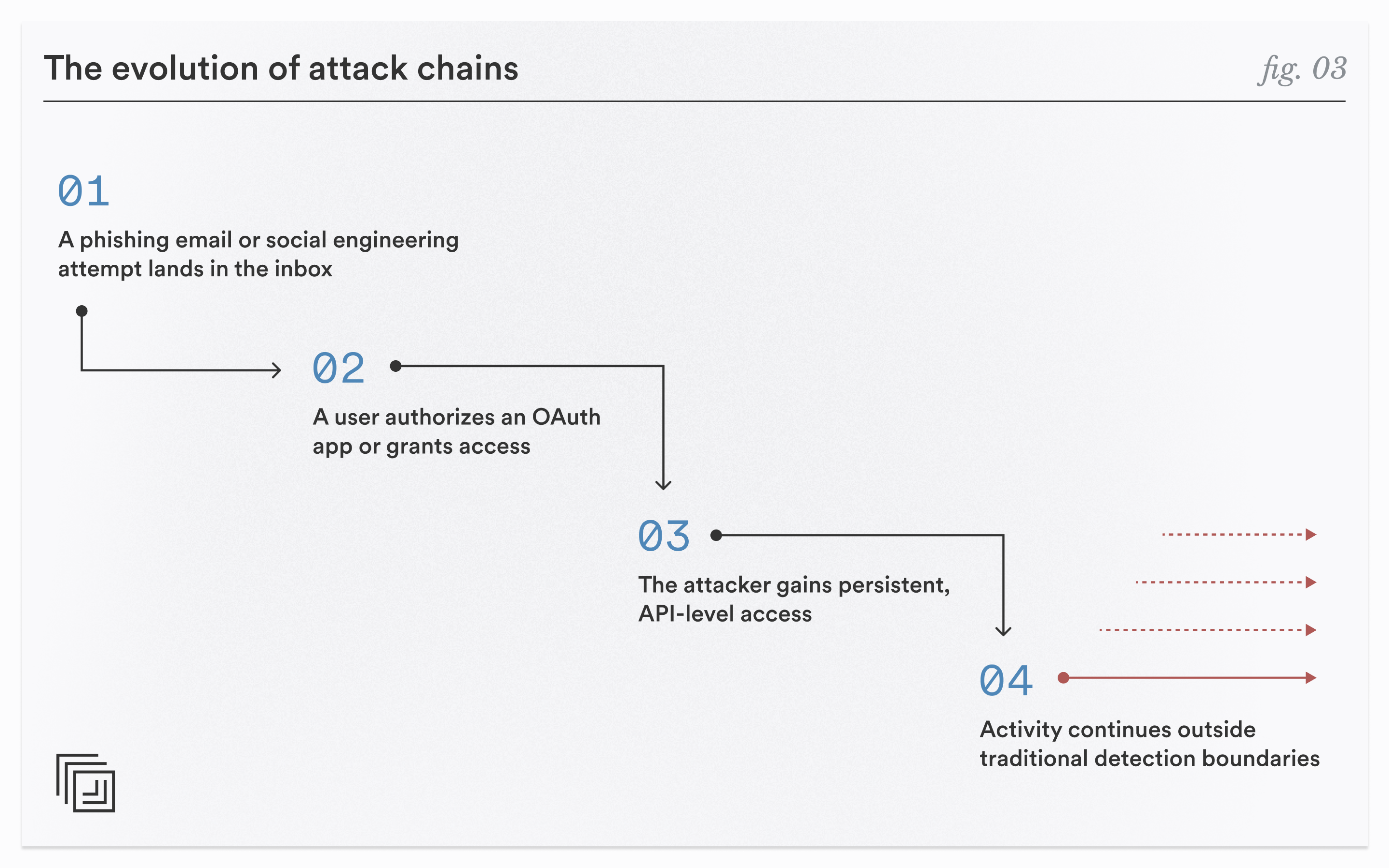
In this example, email is just the starting point. Even more concerning are attacks that bypass email altogether. As demonstrated in the Salesloft / Drift breach in 2025, attackers can steal OAuth tokens from legitimate applications and use them to gain access to a treasure trove of data.
And yet, most security programs are still heavily optimized for phishing alone.
The Next Frontier: OAuth and AI Agents
Security issues aren’t limited to malicious OAuth apps and grant abuse. There’s a new element of risk that comes with the increasing adoption of AI agents, which primarily use OAuth grants to connect non-human identities to company applications. CISOs need to make sure that they understand what apps these agents are connecting to as well as the scopes they’re being given.
The Business Case for Moving Beyond Email
Taken together, this makes a compelling case for CISOs to shift their strategy to address the cloud workspace holistically, not just email security. OAuth apps provide a serious advantage when it comes to ease of connectivity and security can’t become a blocker to AI adoption. But that means addressing some hard truths.
- You can’t secure what you don’t manage. If organizations aren’t actively governing OAuth apps, then a significant portion of enterprise access is effectively unmonitored. That visibility gap is where serious risk lives.
- Manual processes don’t scale with modern risk. OAuth ecosystems are dynamic, user-driven, and constantly evolving. That quarterly audit simply can’t keep up with the speed or volume of change.
- Attackers and AI agents are accelerating the need to address the gap. Persistent connectivity equals persistent risk, and today that risk isn’t just coming from malicious actors anymore.
How Material Is Approaching the Problem
At Material, we see this research as validation of a broader shift. Security can’t stop at detecting malicious emails. It needs to understand how access is granted to apps, monitor how that access is used, and take the appropriate steps when risk is identified. And that needs to happen even in cases where the inbox isn’t involved. In other words, security must follow the attack chain and not stop at the entry point.
Closing the Gap
Security pros know that OAuth risk is rising, and this research shows that organizations are at an inflection point. Awareness is high, the priority is clear, but execution is lagging.
For CISOs, this creates both urgency and opportunity. Those who act now can get ahead of a class of threats that is still under-addressed, but rapidly growing.