The third in a series analyzing HIPAA breach data from the HHS Office for Civil Rights.
TL;DR: 81% of healthcare email breaches exposed fewer than 10,000 patient records. The median breach: 2,737 individuals. Not catastrophic mega-incidents — a constant bleed of mid-size breaches at smaller providers. The industry's fixation on ransomware is obscuring the most common way patient data is actually being exposed.
The headline breaches aren't the whole story
When healthcare security leaders think about email breaches, they think about the big ones. A mammography company exposing 357,000 records. A health data vendor compromising 320,000 individuals. Those are the incidents that make the news and show up in board presentations.
They're not representative of what's actually happening.
Most email breaches are mid-size
Of the 144 email-related HIPAA breaches under investigation by HHS, the vast majority are mid-size incidents at smaller organizations:
- 67% exposed fewer than 5,000 individuals
- 81% exposed fewer than 10,000 individuals
- The median email breach exposed 2,737 patients
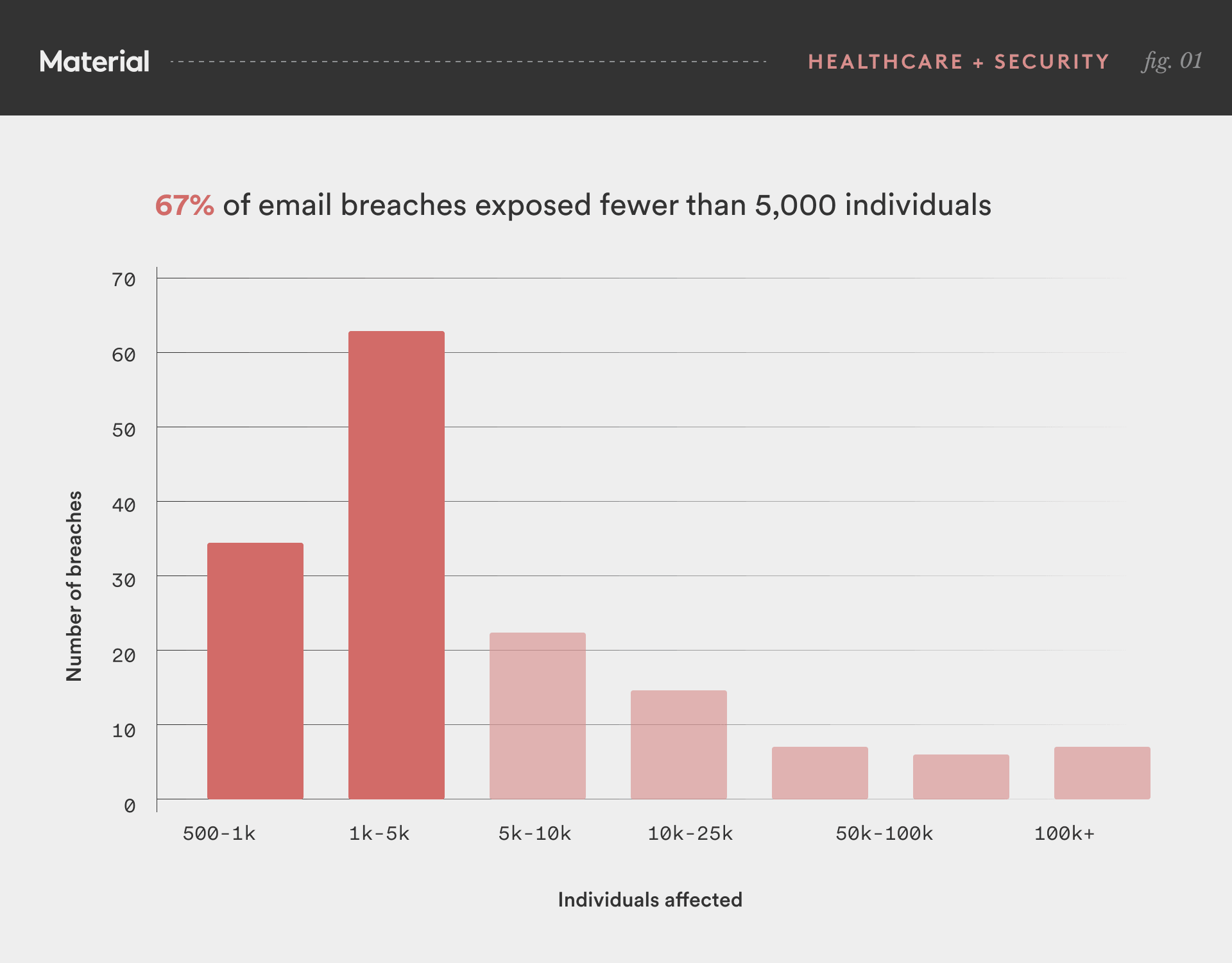
The mean is roughly 13,000 — skewed by a handful of massive business associate breaches. The median tells the real story: the typical healthcare email breach is a regional clinic, a dental practice, a behavioral health provider, or a small hospital where one compromised account exposed a few thousand patients' records.
Why this matters
It's tempting to look at these numbers and feel reassured. A breach affecting 2,700 patients is bad, but it's not existential. The notification costs are containable. The org survives.
That misses the point.
The cumulative impact is enormous. 117 breaches under 10,000 individuals, collectively exposing hundreds of thousands of patient records. No single incident dominates the news, but the aggregate is a slow-moving data exposure crisis. Every one of those patients got a breach notification letter. Every one of those organizations is now on the OCR Breach Portal permanently.
Small breaches have the same root cause as large ones. 83% of email breaches at organizations under 10,000 affected individuals were "Hacking/IT Incident" — the same account takeover pattern as the mega-breaches. Smaller orgs aren't making different mistakes. They're making the same mistake — no controls on data at rest in email — with a smaller blast radius. The breach is smaller because the mailbox had fewer patient messages, not because the security was better.
Email account takeover disproportionately shows up at smaller organizations. The OCR data measures individuals affected, not org size — but when you look at the organizations in the long tail, they're overwhelmingly community health centers, specialty clinics, behavioral health providers, dental practices, and regional hospitals. At big health systems, network server breaches dominate — ransomware, infrastructure compromise. Smaller providers don't have the complex infrastructure that attracts ransomware operators, but they have the same email accounts full of patient data. For many of them, email account takeover is the primary attack surface.
The investment mismatch
The cybersecurity industry — vendors, analysts, media — focuses on large-scale incidents. HIMSS keynotes are about ransomware. Breach reports lead with the biggest numbers. Vendor pitches are calibrated for enterprise health systems with dedicated security teams and seven-figure budgets.
The organizations that appear most frequently in the OCR breach data are community health centers, specialty clinics, behavioral health providers, dental practices, and regional hospitals. Many have one IT person, no dedicated security staff, and an email environment accumulating PHI for years with no controls beyond what Microsoft or Google provides out of the box.
The tools available to these organizations tend to be either enterprise products they can't afford or consumer products that don't address the problem. An email gateway helps with phishing but doesn't protect data at rest. Microsoft Purview exists, but configuring it for retroactive PHI classification across existing mailboxes requires expertise most small healthcare orgs don't have.
The organizations most likely to suffer an email account takeover are the least likely to have controls that limit the damage.
What to do with this
If you're at a larger organization, this data matters for your third-party risk program. Many of these smaller orgs are your business associates, referral partners, or network providers. Their email breach exposes your patients' data.
If you're at one of these smaller organizations, the data is concerning but also clarifying. The threat isn't a sophisticated nation-state attack. It's a compromised credential leading to a mailbox full of patient records with no access controls once someone is authenticated. The fix doesn't need to be complex — it needs to exist.
The industry watches for spectacular failures. The OCR data says the mundane ones are where the damage is actually happening.
This is the third in our series analyzing HIPAA breach data from the HHS Office for Civil Rights. Previous posts: We Analyzed 702 HIPAA Breaches. The Problem Isn't the Phish — It's What's Already in the Inbox and Healthcare's Email Breach Problem Is a Supply Chain Problem. Data source: HHS OCR Breach Portal, breaches under investigation as of March 2026.