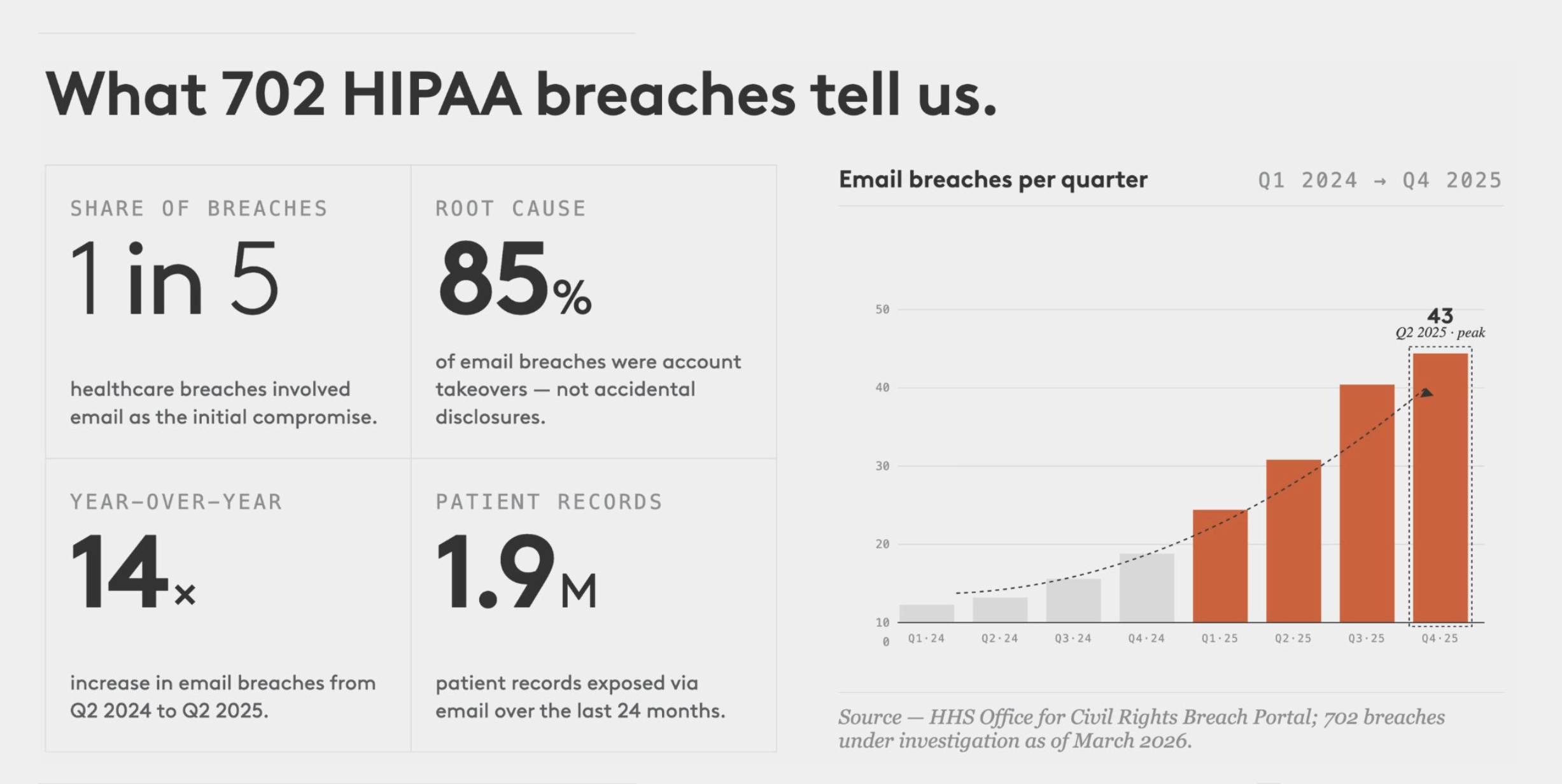
An analysis of 702 HIPAA breaches reported to HHS — and the control gap most organizations are missing.
TL;DR: We analyzed every HIPAA breach currently under investigation by HHS. Email is involved in 1 in 5 healthcare breaches. 85% of those are account takeovers — not accidental disclosures. Nearly 2 million patient records have been exposed through email breaches in the last 24 months alone. Most organizations have strong perimeter defenses but nothing protecting the data already sitting in mailboxes.
Email is healthcare's largest unprotected data repository
Every healthcare organization runs on email. Referral letters, test results, insurance authorizations, patient communications: years of protected health information accumulates in every inbox. When an attacker compromises an email account through phishing or credential theft, they don't just get access to new messages. They get access to everything that account has ever sent or received.
Most organizations have invested in email security gateways that scan inbound messages for malware and phishing links. But once an attacker bypasses the perimeter — through stolen credentials, session hijacking, or social engineering — there is typically no control protecting the data already sitting in the mailbox. The result: a single compromised account can expose thousands of patient records in minutes.
What the OCR breach data shows
We pulled every HIPAA breach currently under investigation from the HHS Office for Civil Rights Breach Portal, comprising 702 breaches affecting 500+ individuals, reported within the last 24 months. Here's what we found.
Email is involved in 1 in 5 healthcare breaches
Of 702 total breaches, 144 involved email as the location of breached information. That makes email the second most common breach vector, behind only network servers (which include ransomware attacks against entire infrastructure). Email breaches are different: they are targeted, they are quiet, and they often go undetected for weeks.
The vast majority are account takeovers
85% of email-related breaches were classified as "Hacking/IT Incident," meaning an external attacker gained unauthorized access to one or more email accounts. This is not accidental disclosure or a misdirected message. This is credential compromise leading to data exfiltration.
The blast radius is massive
The average email breach exposed over 13,000 patient records. The largest single email breach in the dataset, at a Massachusetts-based mammography provider, exposed 357,265 individuals' PHI from email alone.
Healthcare providers bear the brunt
115 of the 144 email breaches (80%) hit healthcare providers directly. Business associates accounted for 22, and health plans for 7. Providers have the highest email volume and the most PHI flowing through inboxes daily.
The cost isn't just the fine, it's everything after
Email breaches trigger a regulatory cascade. Under HIPAA, any breach affecting 500+ individuals must be reported to HHS, to every affected individual, and to media outlets in the state. The organization's name is permanently listed on the OCR Breach Portal.
OCR collected $9.9 million in enforcement penalties in 2024, a 37% jump from the prior year: email-related phishing breaches have been a specific enforcement focus. In April 2025, OCR settled with a California health network for $600,000 after a phishing campaign compromised 45 employee mailboxes and exposed nearly 190,000 individuals' PHI.
Beyond direct fines, IBM's 2024 Cost of a Data Breach Report puts the average healthcare breach cost at $9.48 million. That's more than double the cross-industry average. For email-specific breaches, the bill includes forensic investigation, legal review of every exposed message, individual notification, credit monitoring, and the long tail of litigation.
Why existing controls don't close the gap
Healthcare organizations have invested heavily in perimeter email security. Secure email gateways, anti-phishing training, multi-factor authentication on account login. These are necessary, but they leave a fundamental gap.
Secure email gateways scan inbound messages for threats. They do nothing to protect the PHI already residing in mailboxes. Once an attacker is past the gateway, it's behind them.
Login MFA reduces the likelihood of compromise, but doesn't eliminate it. Session hijacking, MFA fatigue attacks, and adversary-in-the-middle techniques can all bypass login MFA. And once an attacker is in, every message in the account is accessible.
Data loss prevention monitors outbound flows, but isn't designed to protect data at rest inside mailboxes. It can't stop an attacker with legitimate account access from reading historical messages.
The result: organizations protect the front door to email but leave the contents inside unprotected. An attacker who gets past login MFA has unrestricted access to years of PHI, and there's no second line of defense.
What if a compromised account didn't mean compromised data?
The gap in the current security stack is clear: nothing protects sensitive email content after an account is accessed. The data shows what happens when that gap is left open: 144 breaches, nearly 2 million exposed records, and growing regulatory consequences.
At Material Security, we've built a different approach. Instead of only protecting the account login, we protect individual messages that contain sensitive content. Messages with PHI are automatically redacted and require a separate authentication step to view, even for the legitimate account holder.
That means when an attacker compromises an account, they see an inbox, but the sensitive messages are protected. The blast radius is contained. The difference between a reportable breach affecting tens of thousands of patients and no reportable breach at all can come down to whether that second layer of protection was in place.
If your organization is dealing with email account takeover risk, we'd welcome the conversation.